-
The Inefficiency of Legacy Finance For decades, the global financial system relied on legacy payment rails—slow, expensive, and opaque networks built for a pre-digital era. Clearing and settlement often took days, especially across borders, creating massive friction in the increasingly instantaneous Digital Economy. While private FinTech innovations like peer-to-peer (P2P) apps and cryptocurrencies offered glimpses…
-

From Connected Devices to Economic Engine The Internet of Things (IoT) began as a concept centered on simple connected devices—smart thermostats and fitness trackers. Today, it has evolved into a massive, complex ecosystem that is fundamentally restructuring global industries, from manufacturing and logistics to healthcare and energy. This is the IoT Economy—a trillion-dollar domain defined…
-
The Unmet Promise of 5G While 5G technology is still being rolled out globally, promising enhanced speeds and lower latency, the digital world is already looking beyond its capabilities. The current ecosystem is characterized by fragmented coverage, limited true mobility in many rural and developing regions, and a bottleneck on network density required for truly…
-
The New Crisis of Digital Trust The rapid advancement of Generative AI—the same technology that powers creative breakthroughs—has introduced the single greatest threat to digital trust: the Deepfake. Deepfakes are hyper-realistic, AI-generated synthetic media, capable of simulating a person’s voice, appearance, and actions with uncanny accuracy. From sophisticated financial fraud targeting executives to mass political…
-

The Broken Promise of Digital Identity In the current digital ecosystem, our identity is fragmented, controlled, and monetized by large centralized entities. Our passwords, profiles, and data are scattered across thousands of siloed databases managed by tech giants, governments, and banks. This system is fundamentally flawed: it is inconvenient for the user, highly vulnerable to…
-
The Erosion of the Traditional Security Perimeter For decades, digital defense relied on the concept of the “castle-and-moat”: building a strong perimeter firewall to keep threats out while implicitly trusting everything and everyone inside. This model was adequate when corporate data and employees were centralized on-premises. However, the world has fundamentally changed. The post-pandemic shift…
-
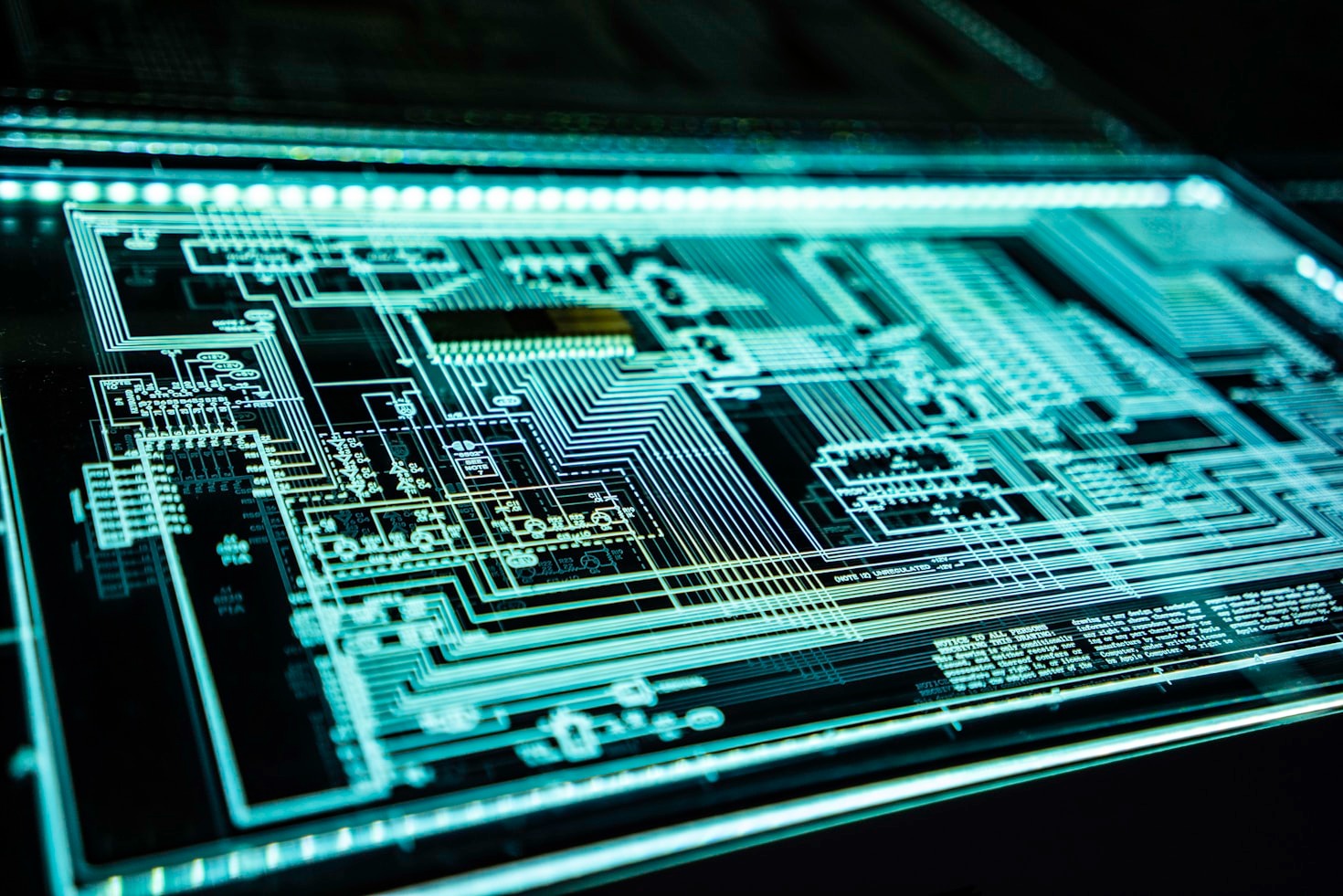
The Centralized Cloud’s Growing Pains For over a decade, the Centralized Cloud—dominated by hyperscalers like AWS, Azure, and Google Cloud—served as the undisputed paradigm for digital infrastructure. It offered unparalleled scalability, convenience, and cost-efficiency by consolidating massive data centers in remote locations. This model successfully powered the internet, SaaS applications, and early mobile computing. However,…
-
On the Brink of a Cryptographic Revolution For decades, the foundations of our digital world—from secure online banking and government secrets to email privacy and cryptocurrency—have rested on the bedrock of Public-Key Cryptography (PKC). These complex mathematical algorithms, notably RSA and Elliptic Curve Cryptography (ECC), rely on the fact that while multiplying large prime numbers…
-

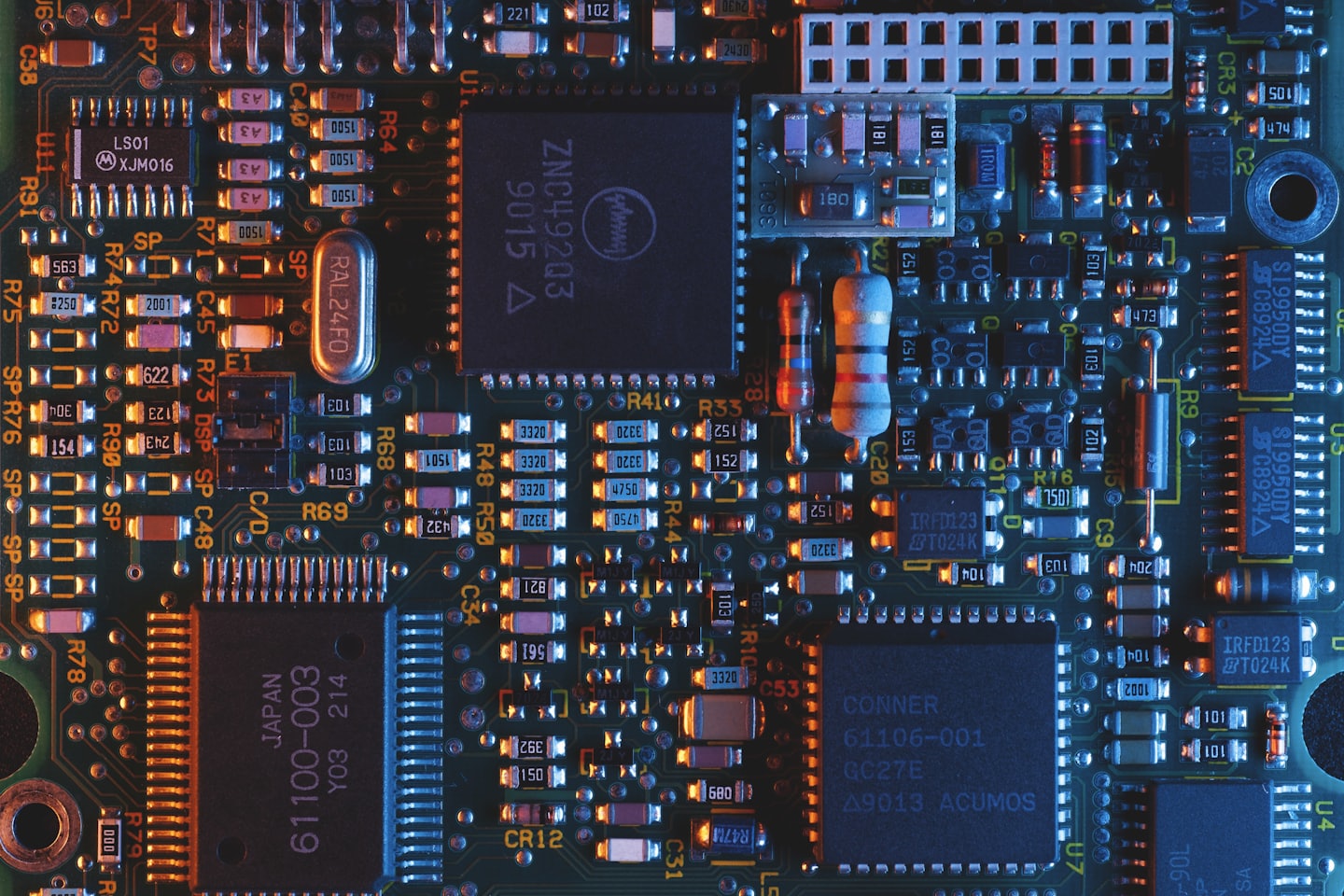
The Quiet Revolution of Connection The Internet of Things (IoT) has transitioned from a futuristic concept to become the backbone of our digital reality. At its core, the Internet of Things is a gigantic network of physical objects embedded with sensors, software, and other technologies for the purpose of connecting and exchanging data with other…
-

Humanity finds itself at a crossroads. On one hand, we witness the peak of technological innovation; on the other, we face the urgent challenges of climate change, resource scarcity, and pollution. The solution to this duality lies in Sustainable Technologies. More than just trends, these innovations represent the intentional design of a better future. They…